
| Home | Info | About Us | FAQ | Contact Us |
Are You Safe from Electronic Snoopers?
|
|
Finally, they could not know that the pleasant young parents worried about their allergic child were actually two more agents. |
Everyone is a target. The experience of the two supermarket demonstrators is far from unique in America today. People in every walk of life, innocent and guilty alike, are finding themselves the targets of the eavesdropper and the busybody.
You are not immune from snoopers. Even though you may not be aware of it, the company that employs you, your business associates and competitors, private detectives, even federal agencies, may be spying on you. The Internal Revenue Service, for example, has prohibited wiretapping since 1938. Despite this, it has trained at least 125 agents in the installation and use of wiretaps. Some corporations have been known to compile extensive dossiers on employees and other persons, using the services of professionals equipped with gadgets that would surprise someone of Ian Fleming's imagination.

|

|

|

|
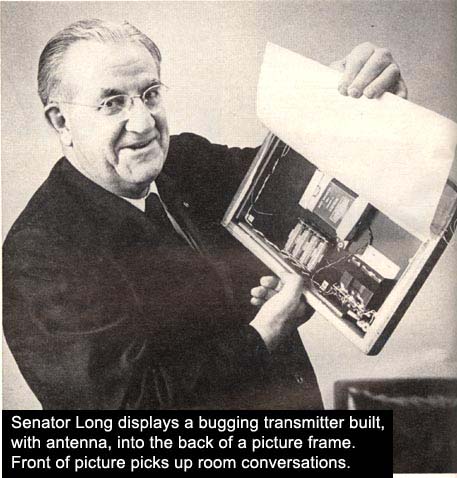
In left hand Sen. Long holds a spike mike, which is fired by a gun into a wall of a building to pick up sounds inside and radio them to snooper. |
Substitute telephone mike not only works normally but, powered by phone current, also radios conversations to listeners-even when phone is not in use. |
Transistor FM transmitter is designed to be carried by agent inside cigarette pack. VHF unit needs only a short antenna, can relay signals up to a mile |
Inside attach� case at top is a receiver and a tape recorder which can be set to receive signals from miniature FM transmitter, preserve them on tape. |
One federal agency, the Federal Bureau of Investigation, has publicly admitted its use of wiretapping year after year. During the past few years, it has usually acknowledged fewer than a hundred taps in operation on the reporting date. Assurances have always been given that these are limited to national-security matters and kidnapping cases, where human life is in danger. Assurances have also been given that each tap is authorized in writing by the Attorney General. The FBI's use of bugs, however, has not been so strictly limited.
Tapping a telephone. Let's take a look at the arsenal of today's snooping equipment. There are three basic methods for tapping a telephone: the direct tap, the indirect or induction-coil tap, and the microphone tap.
When a direct tap is properly installed, only the most careful physical search of the telephone line can possibly locate it. And even then it cannot always be detected. One electronics expert boasted that he could install a tap based on a technique that had remained undetected through more than two dozen inspections. He also told of a tap that would destroy itself if someone either deliberately, or by accident, came too close for comfort. After destruction, there would be no evidence that it had ever existed. The indirect or induction-coil method does not require any connection to the telephone line. It is only necessary to insert such a coil in the magnetic field created by the current on a telephone line. It is normally most effective to find a place where the two wires of the line are separated, and place the coil nearby. The skillful tapper shies from the induction method and is likely to resort to it only if the direct tap will not successfully serve his purpose.
Not long ago, the wiretapper might have to sit for days in a cold basement or in a dusty attic, earphones to his head, transcribing by hand the conversations he overheard. If it was a police tap, a squad of men might be engaged to cover the tap in shifts. Today, a tap can be conveniently monitored by one man. He need only stop by the listening post or "plant" every so often to change the reels on his tape or wire recorder. The new automatic equipment not only provides verbatim transcripts but, to conserve tape, it "listens" and records only when voices are actually on the line.
|
|
|
|
|
In his State of the Union message last January, President Johnson called on Congress to "protect what Justice Brandeis called the right most valued by civilized men-the right to privacy." Shortly thereafter, Senator Edward V. Long of Missouri, who had spent several years studying the problem, introduced the bill recommended by the President: the Right of Privacy Act of 1967. "To put it mildly, electronic anarchy has existed," Long said. "And the victim has been the American people." What is the Right of Privacy Act? Although hearings on it have just been completed and a modified bill will not come to a vote until the end of this year, it would, as currently written, do the following: outlaw wiretapping without the consent of at least one sender or receiver, under penalty of $10,000 fine or five years' imprisonment; make illegal the use of wired microphones or radio transmitters or other devices for eavesdropping under the same penalty. Furthermore, the bill would prohibit the manufacture of any device primarily for wiretapping or eavesdropping when the device has been or will be sent through the mail or transported in interstate commerce. The advertisement of such devices would also be illegal. Only in the interest of national security when authorized by the President of the United States, would electronic surveillance by permissible. "Are You Safe from Electronic Snoopers?" is excerpted from The Intruders, published by Frederick A Praeger, Inc, copyright 1966.
|
Other listening devices. In addition to the wiretap, the snooper has three basic tools: the bug, the radio transmitter, and the recorder. The bug is a concealed or disguised microphone wired into a room to overhear conversation. The transmitter is a combination of a miniature transmitter and a microphone, which may be hidden in a room or carried concealed on the person. The recorder is a combination microphone-recorder which can be concealed on the body or in a briefcase.
The microphone used by a snooper may be the size of a postage stamp or even smaller. It may be hidden in a lamp, a closet, under a rug, or anywhere that wiring can be concealed. Instead of wires, the snooper may decide to use a transmitter, and he can buy one today that is no larger than an aspirin tablet. It may operate by batteries, in which case its life is limited, or be plugged into the house current where it may operate as long as the householder continues to pay his electric bills. In a Senate hearing it was revealed that one such installation was used for 18 months. When retrieved, the transmitter was still operating, relaying conversations perfectly.
Battery-powered transmitters can be concealed almost anywhere, and the smaller they are, the easier their concealment. One transmitter demonstrated before the same Senate committee was hidden in a rose. Another possible hiding place is the dirt surrounding a potted plant.
What happens if the snooper is somehow prevented from gaining access to the target home or office? Because lack of access is more common than access, most of the research on snooping techniques is aimed at the development of techniques that meet this need.
The telephone remains a major ally of the snooper, even when he lacks direct access to it. A recently developed device, when attached to a line at any terminal box, will promptly turn the telephone into a permanent microphone. This sinister adapter is known as an infinity transmitter. It can activate the telephone microphone even though the handpiece is in the cradle. All room conversations can then be monitored.
Bugs and transmitters, as well as wiretaps, are important tools of the snooper who lacks access to the target area. He can place a contact mike on a connecting door; he can place a keyhole extension mike in the door; or, he can slide a small mike under the door. Also handy for the pryer are an electronic stethoscope and a spike mike.
This last is a tiny microphone on the back of a long spike. The spike is inserted in the wall until the point comes in contact with the other wall. In this way, the victim's wall becomes a large sounding board.
In a Louisiana case, it was alleged that the victim had been given a stuffed animal inside which was a small transmitter. This technique obviously requires that the snooper know the victim well enough to justify a gift.
Listening from a distance. So far, all techniques except the wiretap have required access to the building in which the target room is located, if not to the room itself. There are, however, a number of devices and techniques that can be used entirely from outside. A microphone may be hidden just outside a window: A "shotgun" microphone or a microphone with a parabolic reflector will pick up the conversation of persons 500 feet away and will block out all side talk.
The snooper may place a small contact mike on a closed window pane, or he may drive a spike mike into the window frame, with the point just touching the pane. In some cases, this same type of mike can also be driven into the outside wall.
New and more insidious techniques for monitoring rooms without physically entering them are appearing on the market. These techniques include the use of infrared light beams, laser beams, and ultrasonic sound. The infrared and laser techniques hold a potential for monitoring not only what is said but what is done behind closed doors. Both sound and picture would be transmitted from the target area. Already available is a closed-circuit TV camera smaller than a flashlight and concealable, automatic still and movie cameras.
The snooper may easily pursue his interests on the street, in automobiles, and in public places like bars and restaurants. On the street, he may monitor with a shotgun mike and miniature amplifier. A small recorder can now be conveniently carried in a shoulder holster, and a transmitter the size of a pack of cigarettes will, when carried in a pocket, raise no suspicions. A microphone for either of these devices can also be concealed in a tie clip, a button, a wristwatch, or a fountain pen.
There are reports of a transmitter so small that it can fit under a fingernail, but the one the size of a cigarette package is likely to give more satisfactory results. When a transmitter is sending from an automobile, it may be necessary for the snooper to follow in his own car in order to keep the receiver within range. To facilitate tailing, there are devices that can be installed underneath a victim's car, which emit signals. The latest tailing equipment also informs the listener of the general direction in which the tailed car is going.
Fighting back. People who have lived in a police state have discovered reasonably simple ways to foil the snooper. Cover can be provided by turning up the volume of radio or TV set, and talking close together very quietly. In the home, the sound of the shower can drown out normal conversation. A movie theater is a good place to discuss confidential matters, although a subway platform or moving train is even better. The purpose of all of these backdrops is to submerge the conversation in loud background noise.
If snooping is suspected, it is always helpful to be able to disconnect both the telephone and the electric current, but this is not always feasible. In such circumstances an expert countersnooper could use various jamming devices to discourage an eavesdropper.
Several devices for detecting listening devices have been placed on the market, but wiretappers everywhere have been able to sleep soundly in the knowledge that none of these has been completely effective.
We are entitled to ask a few questions at this point. For instance: Who have been the victims of electronic shadowing? Whose privacy has been invaded by the seemingly inexhaustible variety of listening devices?
Here are some answers: In Kansas City, the victims were gambling suspects and two schoolteachers. In Washington D.C., it was Senator Wayne Morse. In Miami, it was the president of a large corporation. In Boston, it was suspected tax-law violators. And this is only a sampling of the number and variety of Americans who have been spied upon by public and private agents.
The guilty and the innocent alike have shared the anonymous attentions of the snoopers. The famous and the infamous, the rich and the poor, the most respected and the least-even you may come within range of a secret ear.



