
The Ways and Means of Bugging
Time, May 28, 1973
In Chicago, ex-Cop Eddie Bray, who heads a private detective agency called American Security Agents, Inc., reports that there has been a 100% increase in one lucrative phase of his operations-"debugging," the detection of hidden devices used to eavesdrop. In New York, John Meyner, president of Sonic Devices, Inc., which also peddles "bug"-finding skills, says he cannot drive through downtown Manhattan without picking up a flood of illegal eavesdropping signals on his sensitive detectors. Just four blocks from the White House, an electronics store name the Spy Shop is doing a thriving business selling both eavesdropping and debugging equipment.
Has the ear of Big Brother become omnipresent in the U.S.? The disclosures of extensive eavesdropping in the Watergate and Pentagon papers cases suggest that it has.
The Nixon Administration, helped into power by its pledge to restore law-and-order, has never made any secret about its intention to use the bug as an anticrime weapon. Former Attorney General John Mitchell justified this policy by saying: "Any citizen of this United States who is not involved in some illegal activity has nothing to fear whatsoever." That would have been scant reassurance for the Congressmen, journalists, FCC employees, campus radicals, black nationalists-and even White House aides-who have been subject to Government wiretaps. Most had engaged in no illegal activity.
The legal authority for Government eavesdropping is murky. As long ago as 1928, in the first wiretapping case to reach the Supreme Court, Justice Louis Brandeis declared that the right to be let alone is "the right most valued by civilized men." His was a minority view, however, and despite the Fourth Amendment's protection against unreasonable search and seizure, the majority held that tapping telephone wires leading into a house was not in itself a breach of the premises or a violation of the owner's privacy.
*
It was not until the '60s that it abandoned the technical, legalistic view of privacy and held that the Fourth Amendment does indeed protect the citizen from wiretapping. In response, Congress enacted the Omnibus Crime Control and Safe Streets Act of 1968, the first federal statute legalizing electronic eavesdropping in investigations of such crimes as treason, robbery, murder as well as bribery and narcotics trafficking-provided that the Government first obtains a court warrant. Since then, local versions of the federal law have been passed in 21 states.
Still, the Federal Government has continued to do some of its bugging without a judge's permission, claiming authority for the taps under the President's oath to "preserve, protect and defend the Constitution" against foreign and domestic enemies. This was the interpretation of the law that allowed the phones of Henry Kissinger's aides to be tapped. Last June, however, in an 8-to-0 decision, the Supreme Court held that such taps could not be used against purely domestic political "suspects" without a warrant.
Under provisions of the 1968 act, ordinary citizens, including private detectives, cannot use bugging devices. The penalty: a fine of $10,000 and/or five years in prison. Nonetheless, the accessibility of new and hard-to-detect eavesdropping gadgetry has encouraged an increasing number of citizens to violate the law. As a result of the miniaturization of modern solid-state electronic equipment, tiny pea-pod-size microphones, transmitters no bigger than a package of cigarettes and other sophisticated gear are available over the counter in ordinary radio stores at prices ranging from a few dollars to thousands. They can readily be adapted for spying and implanted in walls, flowerpots and draperies.
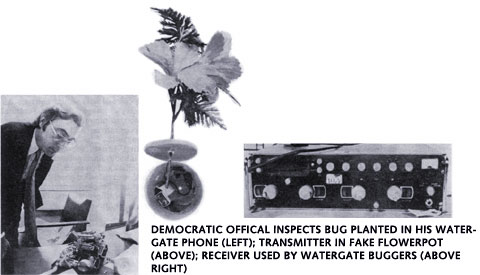
What is surprising about Watergate is that, despite fine equipment, the Republican operatives used such sloppy techniques; they broke into the office of the Democratic National Committee and planted two electronic bugs, consisting of tiny microphones and transmitters that could broadcast a distance of several hundred yards. They hid one in the ceiling, but it failed. The other, intended for Democratic Chairman Lawrence O'Brien's phone, was inadvertently planted in an aide's phone. It was when they returned three weeks later to repair the foul-up and also to take some photographs that they were caught.
According to Columbia University Professor Alan Westin, author of Privacy and Freedom, they could have done a better job without risking entry. One possibility: directional parabolic microphones (like those used by television at sports events) that could have picked up whispers in the Democratic committee rooms from the Howard Johnson's listening post across the street. If the sliding glass door to the terrace was closed, the operatives could conceivably have bounced a laser beam off the glass. Since the pane vibrates from talk in the room, the reflected laser light would have been "imprinted" with this conversation.
|



